Blog
Journey Data: A New Paradigm in Fraud Fighting

Attacker tools have evolved. You deserve an upgrade, too.
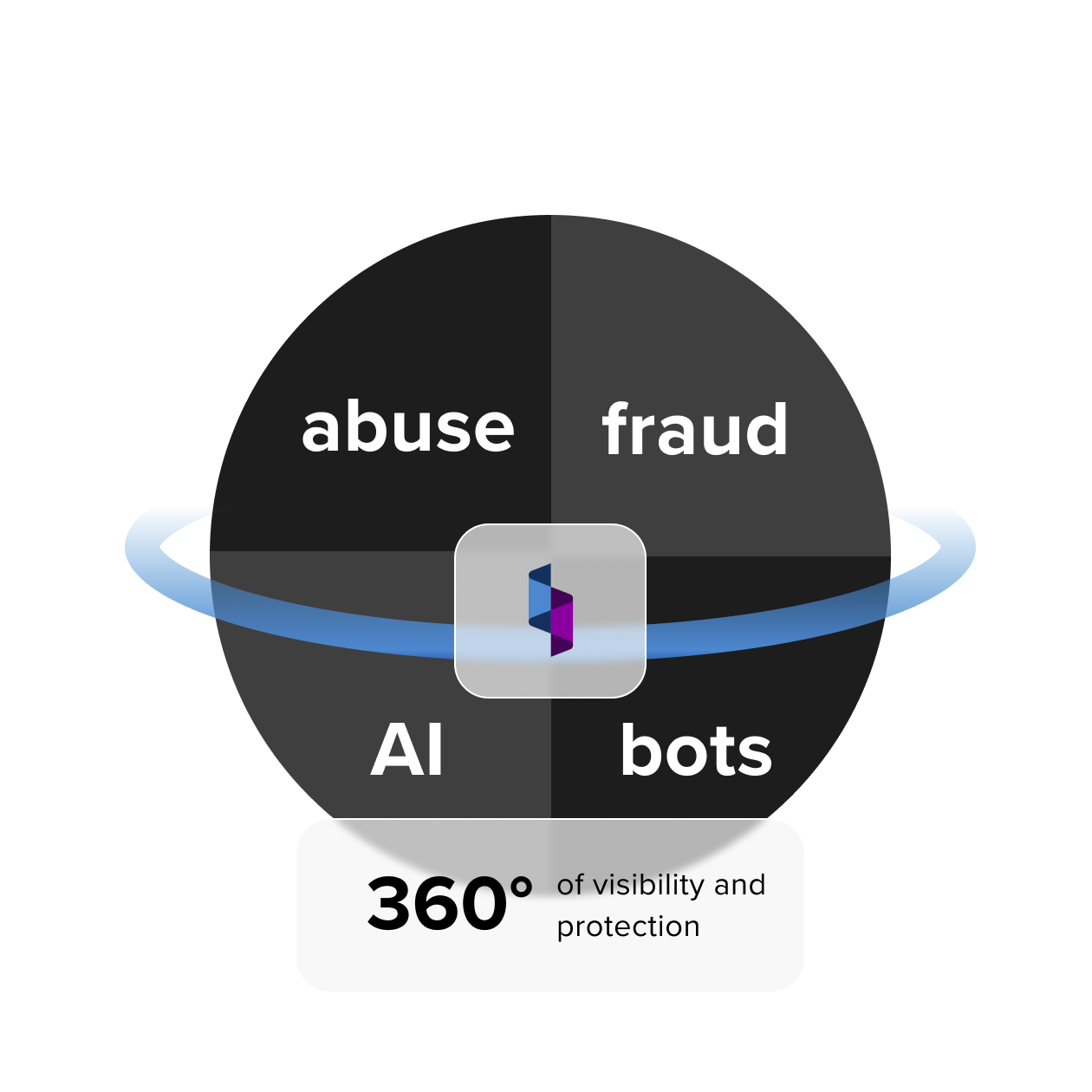
Learn how Spec proactively protects your customer experience from evolving abuse, fraud, AI, and bots.

Blog

Digital customer experiences present a broad attack surface for abuse, fraud, AI, and bots. Instead of managing siloed solutions for each threat, Spec provides a single no-code integration that proactively detects and defends against evolving attacks, leaving attackers with nowhere to hide.
Spec’s patented technology invisibly scans, labels, and actions customer journeys in real time, so you can stay focused on delivering amazing online experiences while we focus on protecting them.
Spec enables us to see what’s happening in our customer flows and respond to new issues quickly – usually within hours.
Get an end-to-end report of your customer journeys and the attack pressure against them.